Quick Links
- 1. Prefer Cold Wallets: (If you do not transact frequently)
- 2. Ensure the correct crypto address
- 3. Multisig Wallets
- 4. Manual safeguarding using Anti Virus and Secure Password
- 5. Allow 2-FA on all your trading accounts and us online wallets from trusted sources
- 6. Backing up the Digital Wallet and Mnemonic Passphrase
- 8. Remove all remote viewing software and set up an Adblocker
- 9. Never let your guard down
The crypto industry has been hit by massive hacking attempts in the past that continue to this day. According to blockchain forensics firm, Chainalysis, crypto hackers stole a record $3.8 billion in 2022, which is 15% up on 2021 ($3.3 billion) and dramatically up on the $0.5 billion stolen in 2020. The first hack happened with Mt GOX when it lost close to 2000 BTC.
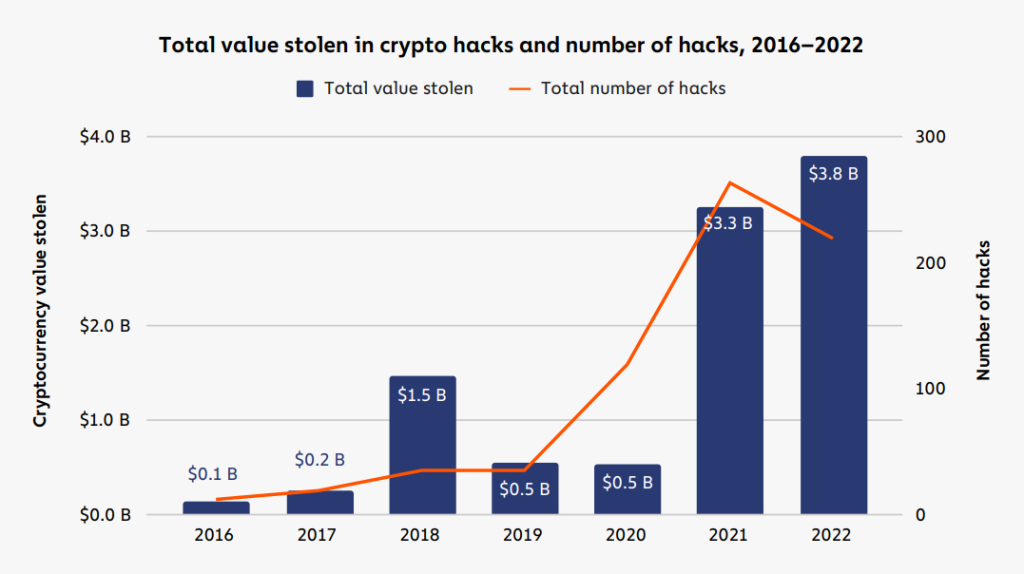
Source: Chainalysis
Crypto trading is profitable if expert and tested crypto trading strategies are used. But before foraying into investing and trading it is imperative to understand the nitty gritty of the ecosystem and avoid putting the crypto wallets in a vulnerable position. In this article, we’ve compiled various ways to secure your crypto assets by fortifying the crypto wallets.
First and the foremost, you need to understand the fundamentals of a cryptocurrency wallet and characteristics. A crypto wallet is governed by typically two cryptographic keys known as Private keys and Public keys.
Private Key:
A private key also called a secret key is alphanumeric in composition and a variable in cryptography which gives your wallet a unique identification that works with an algorithm to encrypt and decrypt code. These keys are only shared with the key’s or the wallet’s generator thus making them highly secure and invincible to hacks thanks to the cryptographic functions working under the hood.. Private keys are confidential and are only shared with its owner and act as a digital ID linking to the wallet. Failing to keep it secure leads to loss of funds as they are a gateway to your crypto assets.
Public Key:
The public key is also an alphanumeric key backed by cryptography that can be claimed and used by anyone to encrypt messages for a specific recipient. It is basically used to receive cryptocurrencies into a user’s account. Both the private and public keys together secure the entire crypto-economy as they are encrypted in the first place and can only be decrypted with the help of the other key the access of which is strictly restricted to the wallet’s owner.
Both the keys are generated once a user initiates a wallet opening request and are stored in the user’s wallet. Each key is responsible for safeguarding a user’s asset while the private key performs important functions such as authorizing the user to spend, withdraw and initiate transactions from their crypto wallets.
Now that we know that it is very important to conceal your private keys, here’s how you can keep your cryptocurrency safe.
Here are the 9 tips to Secure your Cryptocurrency in 2023
1. Prefer Cold Wallets: (If you do not transact frequently)
Cold storage or hardware wallets work the best when one is concerned for cyber threats that are quite rife in the crypto space. Cold wallets are not connected to the internet which makes them inherently invincible to hacks and phishing. These wallets are most sought by users who do not exchange their cryptocurrency too often. Manufacturers such as Trezor and Ledger have different USB look-alike crypto storage devices which are used by many crypto traders, investors and holders. You can ensure your crypto assets safety against cybercriminals and hackers who cannot hack into these cold wallets due to their pre-installed encryption and security features.
2. Ensure the correct crypto address
You should be sure of the recipient’s address when sending them some of your digital currency. Smart hackers can alter the entire address when you paste it in the recipient box and will steal your crypto from right under your nose. Verify it twice before hitting send. If you ever send it to some other address, your crypto is gone forever unless the recipient decides to return you the accidentally sent amount out of honesty.
3. Multisig Wallets
A multisig or Multi-Signature wallet depends on independent approvals before initiating a transaction request and is the safest form of security for cryptocurrency. It requires at least two different signatures to authorize a transaction. As high as 3–5 signatures signing, it makes your crypto account extremely safe against hacks and unwanted withdrawals. Some of the best Multisig wallets are mentioned below:
Castle
UniPass
Cashmere
4. Manual safeguarding using Anti Virus and Secure Password
When you have a lot of worth in crypto, you should really be having a great firewall to fortify your computer against cyber and malware attacks. Hackers can inject malicious viruses in your computer and secretly retrieve all your information using their underhand tactics. The best to prevent that is to use a Rated R antivirus such as Norton or Bitdefender.
Use a good password generator that can create up to 64 character passwords with numbers, lowercase and uppercase letters and symbols. Avoid using simple passwords as you use on social media sites and apps. It is your crypto and your responsibility. Hackers use sophisticated malware and password crackers that are created to do just that; empty your online pockets. So, the complex your password is, the more difficult it will be to crack it. You can use one of the password managers mentioned below to create an automatic yet strong password. Always use a unique password for your wallets as a study revealed those passwords which are slightly changed and used are at high risk all the time.
5. Allow 2-FA on all your trading accounts and us online wallets from trusted sources
Multi-factor authentication is a powerful tactic to prevent any harm to your crypto trading accounts or crypto wallets. Applications such as Authy and Google Authenticator will enable an additional layer of verification through your email or phone number when you initiate a login request to your account. It is a simple yet effective method as it gives you full control of your account when logging in.
In this digital age, anything can be virtually recreated. Hackers can create similar copies of online wallets and repurpose them to store your crypto, it’s only that you will willingly give them all your crypto without even knowing it. Always look for trusted sources before downloading anything that will make you regret your decision later.
Some of the best Multi-currency crypto wallets are mentioned below:
Exodus: Desktop
FreeWallet: Web
Guarda: Web
Atomic Wallet: Desktop
6. Backing up the Digital Wallet and Mnemonic Passphrase
In case everything goes wrong, you can always create a backup file for your wallet the instruction of which will be available on wallet provider websites. You can always resume your wallet access through a backup phrase or file in a few steps. But remember, it is only for getting access to a locked account and not lost funds. If you lose your crypto once there is absolutely no way to recover them.
Write down your backup phrase or the seed phrase on a piece of paper or save it online or on your mobile phone to gain access to your wallet in case you get logged out and forget the password. The seed phrase is a series of disparate phrases made of 6–12 random words such as kite, creek, last, again etc as shown in the image above. You can type it in order if you lose access to your account and can resume its functions after creating a new password.
7. Check your destination website link
Crosscheck the website you are on at a given time if it has the authentic link like always. Hackers can copy an entire website and lure you to log in to your wallet just to steal your credentials and empty your crypto. The phishing website is strikingly similar to the authentic one and this is where users have to verify the URL and its spelling above to reveal its true identity. Checking a website’s SSL certificate will also help in identifying its authenticity. If you see a secure connection represented in green, you’re good to go. If not, Google will flag the website beforehand to prevent any harm.
8. Remove all remote viewing software and set up an Adblocker
Remote viewing software such as Teamviewer can alter your privacy settings and rewrite your preferences as they are meant to provide entire access to your computer to a remote device stationed anywhere across the world.
It is clear that this software can interfere with your privacy and allow access to a remote device hence contributing to funds getting drained.
Ads are a great mess too when you are using your computer but sometimes they can be even worse as they can carry harmful trojans aimed at stealing all your information for transferring it all to a hacker sitting in his basement and looking for easy money. If you accidentally click on any such ads, hackers might steal all your personal info including your private and public keys thus leaving no trace of your crypto.
9. Never let your guard down

Always keep an eye on your cryptocurrency stored across your wallets. Access your wallets frequently to view its contents and if your storage is as intact as the previous time you saw it. It will help you catch any instance of forgery or dishonest activity before it’s too late. Something so volatile and vulnerable should be kept in close proximity for instant viewing. This way you will come to know the frequently changing value of your crypto and keep it in supervision at all times.
So these are the major practices you can follow if you want to ward off any potential threats you don’t want bugging you all the time. By following the tips you can never worry about your crypto getting drained EVER!
You can also go on reading the enormous size of the total volume of trade occurring on crypto exchanges throughout the world in this article. Readers can grasp a sound understanding of the total worth of the billions of dollars flowing in and out of these exchanges and how much of its worth is lost to scams, frauds, and hacks.
In the next series of this article, we will create a walkthrough to help our users create wallets for some popular cryptocurrencies. The successive article will walk you through different major wallets with their unique benefits and pros and cons such as Storing multiple cryptocurrencies, custodial & non-custodial wallets and more.